Prep Test: Questions 91-180
Quiz Summary
0 of 87 Questions completed
Questions:
Information
You have already completed the quiz before. Hence you can not start it again.
Quiz is loading…
You must sign in or sign up to start the quiz.
You must first complete the following:
Results
Results
0 of 87 Questions answered correctly
Your time:
Time has elapsed
You have reached 0 of 0 point(s), (0)
Earned Point(s): 0 of 0, (0)
0 Essay(s) Pending (Possible Point(s): 0)
Categories
- Not categorized 0%
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- Current
- Review
- Answered
- Correct
- Incorrect
-
Question 1 of 87
1. Question
Question 91
Which of the following describes the BEST approach for deploying application patches?
CorrectIncorrect -
Question 2 of 87
2. Question
Question 92
A security analyst is investigating an incident that was first reported as an issue connecting to network shares and the Internet. While reviewing logs and tool output, the analyst sees the following:
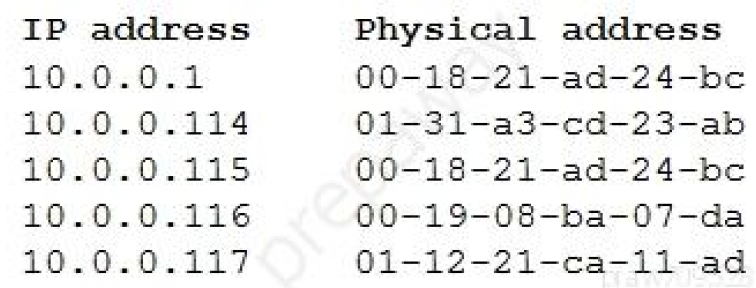
Which of the following attacks has occurred?
CorrectIncorrect -
Question 3 of 87
3. Question
Question 93
After entering a username and password, an administrator must draw a gesture on a touch screen. Which of the following demonstrates what the administrator is providing?
CorrectIncorrect -
Question 4 of 87
4. Question
Question 94
An organization suffered an outage, and a critical system took 90 minutes to come back online. Though there was no data loss during the outage, the expectation was that the critical system would be available again within 60 minutes. Which of the following is the 60-minute expectation an example of?
CorrectIncorrect -
Question 5 of 87
5. Question
Question 95
Joe, a user at a company, clicked an email links that led to a website that infected his workstation. Joe was connected to the network, and the virus spread to the network shares. The protective measures failed to stop this virus, and it has continued to evade detection. Which of the following should a security administrator implement to protect the environment from this malware?
CorrectIncorrect -
Question 6 of 87
6. Question
Question 96
An organization is concerned that its hosted web servers are not running the most updated version of the software. Which of the following would work BEST to help identify potential vulnerabilities?
CorrectIncorrect -
Question 7 of 87
7. Question
Question 97
A retail executive recently accepted a job with a major competitor. The following week, a security analyst reviews the security logs and identifies successful logon attempts to access the departed executive’s accounts. Which of the following security practices would have addressed the issue?
CorrectIncorrect -
Question 8 of 87
8. Question
Question 98
A security analyst is performing a forensic investigation involving compromised account credentials. Using the Event Viewer, the analyst was able to detect the following message: ‘Special privileges assigned to new logon.’
Several of these messages did not have a valid logon associated with the user before these privileges were assigned. Which of the following attacks is MOST likely being detected?
CorrectIncorrect -
Question 9 of 87
9. Question
Question 99
A systems administrator needs to implement an access control scheme that will allow an object’ access policy to be determined by its owner. Which of the following access control schemes BEST fits the requirements?
CorrectIncorrect -
Question 10 of 87
10. Question
Question 100
A cybersecurity analyst reviews the log files from a web server and sees a series of files that indicate a directory-traversal attack has occurred. Which of the following is the analyst MOST likely seeing?
CorrectIncorrect -
Question 11 of 87
11. Question
Question 101
A company has limited storage space available and an online presence that cannot be down for more than four hours. Which of the following backup methodologies should the company implement to allow for the FASTEST database restore time in the event of a failure, while being mindful of the limited available storage space?
CorrectIncorrect -
Question 12 of 87
12. Question
Question 102
An organization has a growing workforce that is mostly driven by additions to the sales department. Each newly hired salesperson relies on a mobile device to conduct business. The Chief Information Officer (CIO) is wondering if the organization may need to scale down just as quickly as it scaled up. The CIO is also concerned about the organization’s security and customer privacy. Which of the following would be BEST to address the CIO’s concerns?
CorrectIncorrect -
Question 13 of 87
13. Question
Question 103
A malicious actor recently penetrated a company’s network and moved laterally to the datacenter. Upon investigation, a forensics firm wants to know what was in the memory on the compromised server. Which of the following files should be given to the forensics firm?
CorrectIncorrect -
Question 14 of 87
14. Question
Question 104
A public relations team will be taking a group of guests on a tour through the facility of a large e-commerce company. The day before the tour, the company sends out an email to employees to ensure all whiteboards are cleaned and all desks are cleared. The company is MOST likely trying to protect against:
CorrectIncorrect -
Question 15 of 87
15. Question
Question 105
The manager who is responsible for a data set has asked a security engineer to apply encryption to the data on a hard disk. The security engineer is an example of a:
CorrectIncorrect -
Question 16 of 87
16. Question
Question 106
A network engineer is troubleshooting wireless network connectivity issues that were reported by users. The issues are occurring only in the section of the building that is closest to the parking lot. Users are intermittently experiencing slow speeds when accessing websites and are unable to connect to network drives. The issues appear to increase when laptop users return to their desks after using their devices in other areas of the building. There have also been reports of users being required to enter their credentials on web pages in order to gain access to them. Which of the following is the MOST likely cause of this issue?
CorrectIncorrect -
Question 17 of 87
17. Question
Question 107
A security administrator needs to create a RAID configuration that is focused on high read speeds and fault tolerance. It is unlikely that multiple drives will fail simultaneously. Which of the following RAID configurations should the administrator use?
CorrectIncorrect -
Question 18 of 87
18. Question
Question 108
A company’s Chief Information Officer (CIO) is meeting with the Chief Information Security Officer (CISO) to plan some activities to enhance the skill levels of the company’s developers. Which of the following would be MOST suitable for training the developers?
CorrectIncorrect -
Question 19 of 87
19. Question
Question 109
A security analyst needs to generate a server certificate to be used for 802.1X and secure RDP connections. The analyst is unsure what is required to perform the task and solicits help from a senior colleague. Which of the following is the FIRST step the senior colleague will most likely tell the analyst to perform to accomplish this task?
CorrectIncorrect -
Question 20 of 87
20. Question
Question 110
Under GDPR, which of the following is MOST responsible for the protection of privacy and website user rights?
CorrectIncorrect -
Question 21 of 87
21. Question
Question 110
A small business just recovered from a ransomware attack against its file servers by purchasing the decryption keys from the attackers. The issue was triggered by a phishing email and the IT administrator wants to ensure it does not happen again. Which of the following should the IT administrator do FIRST after recovery?
CorrectIncorrect -
Question 22 of 87
22. Question
Question 112
A global pandemic is forcing a private organization to close some business units and reduce staffing at others. Which of the following would be BEST to help the organization’s executives determine their next course of action?
CorrectIncorrect -
Question 23 of 87
23. Question
Question 113
Which of the following describes the ability of code to target a hypervisor from inside a guest OS?
CorrectIncorrect -
Question 24 of 87
24. Question
Question 114
After a ransomware attack, a forensics company needs to review a cryptocurrency transaction between the victim and the attacker. Which of the following will the company MOST likely review to trace this transaction?
CorrectIncorrect -
Question 25 of 87
25. Question
Question 115
During an incident response, a security analyst observes the following log entry on the web server:
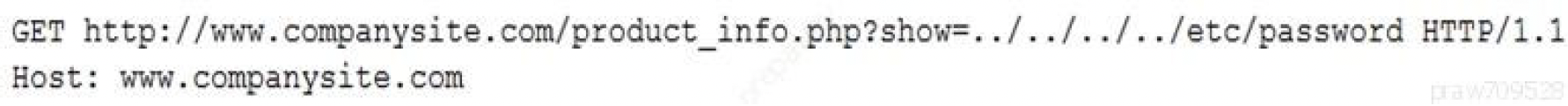
Which of the following BEST describes the type of attack the analyst is experiencing?
CorrectIncorrect -
Question 26 of 87
26. Question
Question 116
Which of the following ISO standards is certified for privacy?
CorrectIncorrect -
Question 27 of 87
27. Question
Question 117
A document that appears to be malicious has been discovered in an email that was sent to a company’s Chief Financial Officer (CFO). Which of the following would be BEST to allow a security analyst to gather information and confirm it is a malicious document without executing any code it may contain?
CorrectIncorrect -
Question 28 of 87
28. Question
Question 118
A security analyst is running a vulnerability scan to check for missing patches during a suspected security incident. During which of the following phases of the response process is this activity MOST likely occurring?
CorrectIncorrect -
Question 29 of 87
29. Question
Question 119
Which of the following is a team of people dedicated to testing the effectiveness of organizational security programs by emulating the techniques of potential attackers?
CorrectIncorrect -
Question 30 of 87
30. Question
Question 120
A security analyst discovers that a company’s username and password database was posted on an Internet forum. The usernames and passwords are stored in plain text. Which of the following would mitigate the damage done by this type of data exfiltration in the future?
CorrectIncorrect -
Question 31 of 87
31. Question
Question 121
Which of the following are requirements that must be configured for PCI DSS compliance? (Choose two.)
CorrectIncorrect -
Question 32 of 87
32. Question
Question 122
A security analyst needs to be proactive in understanding the types of attacks that could potentially target the company’ executives. Which of the following intelligence sources should the security analyst review?
CorrectIncorrect -
Question 33 of 87
33. Question
Question 123
A security audit has revealed that a process control terminal is vulnerable to malicious users installing and executing software on the system. The terminal is beyond end-of-life support and cannot be upgraded, so it is placed on a protected network segment. Which of the following would be MOST effective to implement to further mitigate the reported vulnerability?
CorrectIncorrect -
Question 34 of 87
34. Question
Question 124
A user recently entered a username and password into a recruiting application website that had been forged to look like the legitimate site. Upon investigation, a security analyst identifies the following:
✑ The legitimate website’s IP address is 10.1.1.20 and eRecruit.local resolves to this IP.
✑ The forged website’s IP address appears to be 10.2.12.99, based on NetFlow records.
✑ All three of the organization’s DNS servers show the website correctly resolves to the legitimate IP.
✑ DNS query logs show one of the three DNS servers returned a result of 10.2.12.99 (cached) at the approximate time of the suspected compromise.
Which of the following MOST likely occurred?
CorrectIncorrect -
Question 35 of 87
35. Question
Question 125
An organization has hired a security analyst to perform a penetration test. The analyst captures 1Gb worth of inbound network traffic to the server and transfers the pcap back to the machine for analysis. Which of the following tools should the analyst use to further review the pcap?
CorrectIncorrect -
Question 36 of 87
36. Question
Question 126
A company uses wireless for all laptops and keeps a very detailed record of its assets, along with a comprehensive list of devices that are authorized to be on the wireless network. The Chief Information Officer (CIO) is concerned about a script kiddie potentially using an unauthorized device to brute force the wireless PSK and obtain access to the internal network. Which of the following should the company implement to BEST prevent this from occurring?
CorrectIncorrect -
Question 37 of 87
37. Question
Question 127
A vulnerability assessment report will include the CVSS score of the discovered vulnerabilities because the score allows the organization to better:
CorrectIncorrect -
Question 38 of 87
38. Question
Question 128
A security engineer is reviewing log files after a third party discovered usernames and passwords for the organization’s accounts. The engineer sees there was a change in the IP address for a vendor website one week earlier. This change lasted eight hours. Which of the following attacks was MOST likely used?
CorrectIncorrect -
Question 39 of 87
39. Question
Question 129
A company recently moved sensitive videos between on-premises, company-owned websites. The company then learned the videos had been uploaded and shared to the Internet. Which of the following would MOST likely allow the company to find the cause?
CorrectIncorrect -
Question 40 of 87
40. Question
Question 130
A large industrial system’s smart generator monitors the system status and sends alerts to third-party maintenance personnel when critical failures occur. While reviewing the network logs, the company’s security manager notices the generator’s IP is sending packets to an internal file server’s IP. Which of the following mitigations would be BEST for the security manager to implement while maintaining alerting capabilities?
CorrectIncorrect -
Question 41 of 87
41. Question
Question 131
Which of the following allows for functional test data to be used in new systems for testing and training purposes to protect the real data?
CorrectIncorrect -
Question 42 of 87
42. Question
Question 132
A consultant is configuring a vulnerability scanner for a large, global organization in multiple countries. The consultant will be using a service account to scan systems with administrative privileges on a weekly basis, but there is a concern that hackers could gain access to the account and pivot throughout the global network. Which of the following would be BEST to help mitigate this concern?
CorrectIncorrect -
Question 43 of 87
43. Question
Question 133
A software developer needs to perform code-execution testing, black-box testing, and non-functional testing on a new product before its general release. Which of the following BEST describes the tasks the developer is conducting?
CorrectIncorrect -
Question 44 of 87
44. Question
Question 134
A security analyst is configuring a large number of new company-issued laptops. The analyst received the following requirements:
✑ The devices will be used internationally by staff who travel extensively.
✑ Occasional personal use is acceptable due to the travel requirements.
✑ Users must be able to install and configure sanctioned programs and productivity suites.
✑ The devices must be encrypted.
✑ The devices must be capable of operating in low-bandwidth environments.
Which of the following would provide the GREATEST benefit to the security posture of the devices?
CorrectIncorrect -
Question 45 of 87
45. Question
Question 135
An organization has decided to host its web application and database in the cloud. Which of the following BEST describes the security concerns for this decision?
CorrectIncorrect -
Question 46 of 87
46. Question
Question 136
An organization that is located in a flood zone is MOST likely to document the concerns associated with the restoration of IT operations in a:
CorrectIncorrect -
Question 47 of 87
47. Question
Question 137
A user received an SMS on a mobile phone that asked for bank details. Which of the following social-engineering techniques was used in this case?
CorrectIncorrect -
Question 48 of 87
48. Question
Question 138
Company engineers regularly participate in a public Internet forum with other engineers throughout the industry. Which of the following tactics would an attacker MOST likely use in this scenario?
CorrectIncorrect -
Question 49 of 87
49. Question
Question 139
Which of the following will provide the BEST physical security countermeasures to stop intruders? (Choose two.)
CorrectIncorrect -
Question 50 of 87
50. Question
Question 140
A security analyst is looking for a solution to help communicate to the leadership team the severity levels of the organization’s vulnerabilities. Which of the following would BEST meet this need?
CorrectIncorrect -
Question 51 of 87
51. Question
Question 141
A security incident may have occurred on the desktop PC of an organization’s Chief Executive Officer (CEO). A duplicate copy of the CEO’s hard drive must be stored securely to ensure appropriate forensic processes and the chain of custody are followed. Which of the following should be performed to accomplish this task?
CorrectIncorrect -
Question 52 of 87
52. Question
Question 142
The Chief Executive Officer (CEO) of an organization would like staff members to have the flexibility to work from home anytime during business hours, including during a pandemic or crisis. However, the CEO is concerned that some staff members may take advantage of the flexibility and work from high-risk countries while on holiday or outsource work to a third-party organization in another country. The Chief Information Officer (CIO) believes the company can implement some basic controls to mitigate the majority of the risk. Which of the following would be BEST to mitigate the CEO’s concerns? (Choose two.)
CorrectIncorrect -
Question 53 of 87
53. Question
Question 143
In the middle of a cyberattack, a security engineer removes the infected devices from the network and locks down all compromised accounts. In which of the following incident response phases is the security engineer currently operating?
CorrectIncorrect -
Question 54 of 87
54. Question
Question 144
The SOC is reviewing processes and procedures after a recent incident. The review indicates it took more than 30 minutes to determine that quarantining an infected host was the best course of action. This allowed the malware to spread to additional hosts before it was contained. Which of the following would be BEST to improve the incident response process?
CorrectIncorrect -
Question 55 of 87
55. Question
Question 145
A security analyst is reviewing the following attack log output:
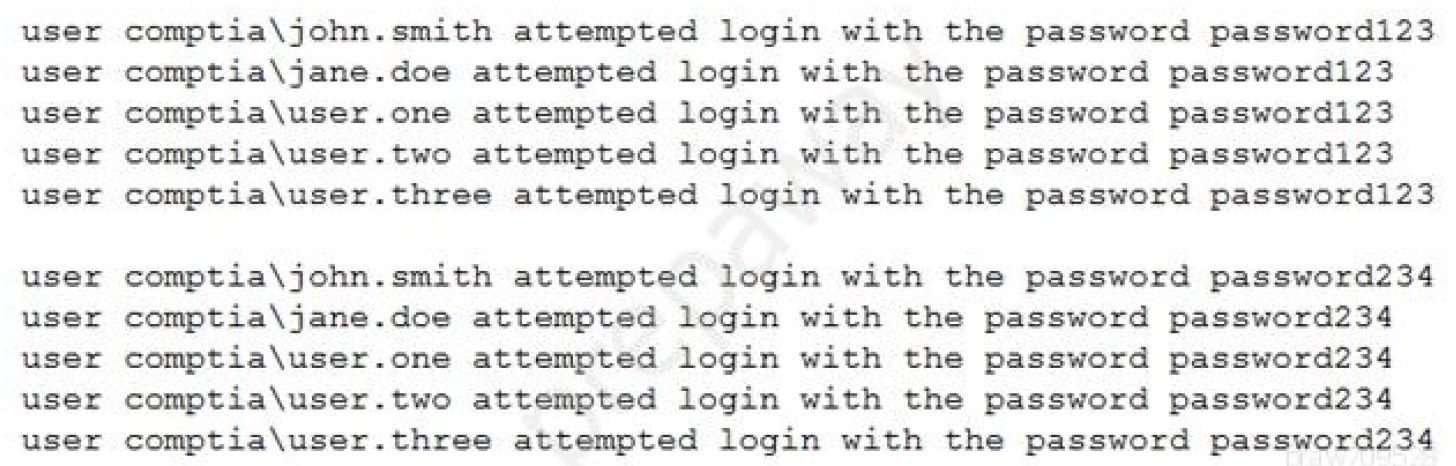
Which of the following types of attacks does this MOST likely represent?
CorrectIncorrect -
Question 56 of 87
56. Question
Question 146
A network administrator is setting up wireless access points in all the conference rooms and wants to authenticate devices using PKI. Which of the following should the administrator configure?
CorrectIncorrect -
Question 57 of 87
57. Question
Question 147
Which of the following are the MOST likely vectors for the unauthorized or unintentional inclusion of vulnerable code in a software company’s final software releases? (Choose two.)
CorrectIncorrect -
Question 58 of 87
58. Question
Question 148
A recent audit uncovered a key finding regarding the use of a specific encryption standard in a web application that is used to communicate with business customers. Due to the technical limitations of its customers, the company is unable to upgrade the encryption standard. Which of the following types of controls should be used to reduce the risk created by this scenario?
CorrectIncorrect -
Question 59 of 87
59. Question
Question 149
An organization just experienced a major cyberattack incident. The attack was well coordinated, sophisticated, and highly skilled. Which of the following targeted the organization?
CorrectIncorrect -
Question 60 of 87
60. Question
Question 150
A security analyst has received an alert about PII being sent via email. The analyst’s Chief Information Security Officer (CISO) has made it clear that PII must be handled with extreme care. From which of the following did the alert MOST likely originate?
CorrectIncorrect -
Question 61 of 87
61. Question
Question 152
An enterprise has hired an outside security firm to conduct penetration testing on its network and applications. The firm has been given all the developer’s documentation about the internal architecture. Which of the following BEST represents the type of testing that will occur?
CorrectIncorrect -
Question 62 of 87
62. Question
Question 153
An enterprise has hired an outside security firm to conduct penetration testing on its network and applications. The firm has been given all the developer’s documentation about the internal architecture. Which of the following BEST represents the type of testing that will occur?
CorrectIncorrect -
Question 63 of 87
63. Question
Question 154
A security engineer has enabled two-factor authentication on all workstations. Which of the following approaches are the MOST secure? (Choose two.)
CorrectIncorrect -
Question 64 of 87
64. Question
Question 155
A security analyst needs to determine how an attacker was able to use User3 to gain a foothold within a company ג€™s network. The company’s lockout policy requires that an account be locked out for a minimum of 15 minutes after three unsuccessful attempts. While reviewing the log files, the analyst discovers the following:
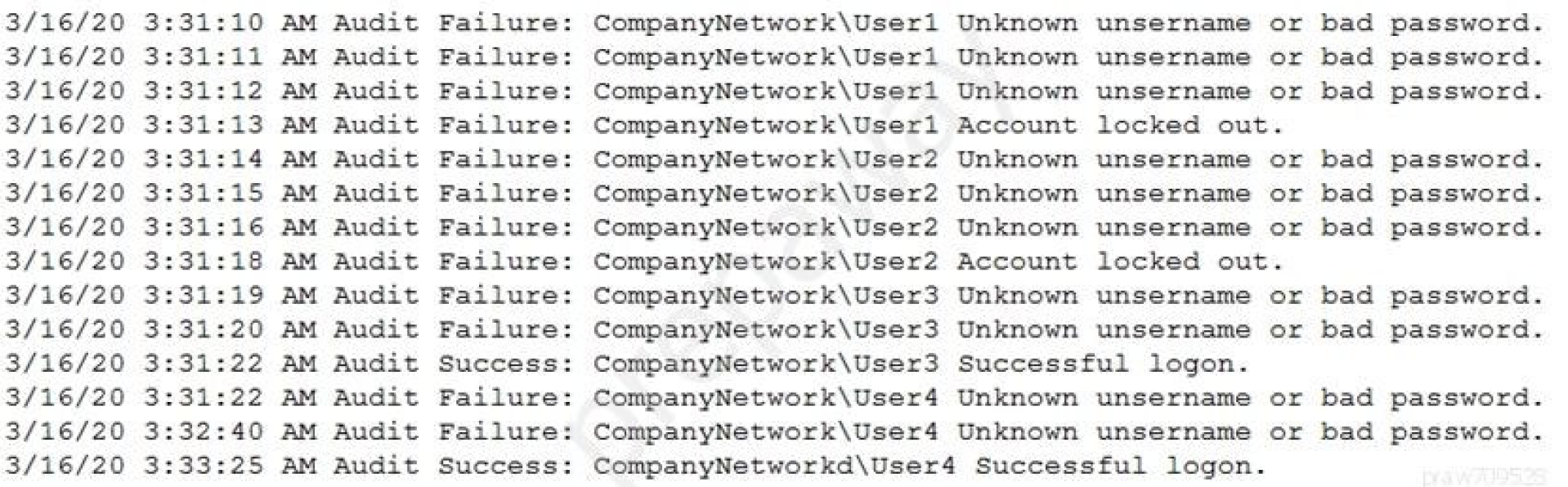
Which of the following attacks MOST likely occurred?
CorrectIncorrect -
Question 65 of 87
65. Question
Question 157
Which of the following technical controls is BEST suited for the detection and prevention of buffer overflows on hosts?
CorrectIncorrect -
Question 66 of 87
66. Question
Question 158
A Chief Information Security Officer (CISO) is concerned about the organization’s ability to continue business operations in the event of a prolonged DDoS attack on its local datacenter that consumes database resources. Which of the following will the CISO MOST likely recommend to mitigate this risk?
CorrectIncorrect -
Question 67 of 87
67. Question
Question 160
Which of the following will MOST likely cause machine-learning and AI-enabled systems to operate with unintended consequences?
CorrectIncorrect -
Question 68 of 87
68. Question
Question 159
A local coffee shop runs a small WiFi hotspot for its customers that utilizes WPA2-PSK. The coffee shop would like to stay current with security trends and wants to implement WPA3 to make its WiFi even more secure. Which of the following technologies will the coffee shop MOST likely use in place of PSK?
CorrectIncorrect -
Question 69 of 87
69. Question
Question 161
The process of passively gathering information prior to launching a cyberattack is called:
CorrectIncorrect -
Question 70 of 87
70. Question
Question 162
During a routine scan of a wireless segment at a retail company, a security administrator discovers several devices are connected to the network that do not match the company’s naming convention and are not in the asset inventory. WiFi access is protected with 256-bit encryption via WPA2. Physical access to the company’s facility requires two-factor authentication using a badge and a passcode. Which of the following should the administrator implement to find and remediate the issue? (Choose two.)
CorrectIncorrect -
Question 71 of 87
71. Question
Question 163
An organization has various applications that contain sensitive data hosted in the cloud. The company’s leaders are concerned about lateral movement across applications of different trust levels. Which of the following solutions should the organization implement to address the concern?
CorrectIncorrect -
Question 72 of 87
72. Question
Question 164
A security engineer at an offline government facility is concerned about the validity of an SSL certificate. The engineer wants to perform the fastest check with the least delay to determine if the certificate has been revoked. Which of the following would BEST meet these requirements?
CorrectIncorrect -
Question 73 of 87
73. Question
Question 165
A small retail business has a local store and a newly established and growing online storefront. A recent storm caused a power outage to the business and the local ISP, resulting in several hours of lost sales and delayed order processing. The business owner now needs to ensure two things:
✑ Protection from power outages
✑ Always-available connectivity in case of an outage The owner has decided to implement battery backups for the computer equipment.
Which of the following would BEST fulfill the owner’s second need?
CorrectIncorrect -
Question 74 of 87
74. Question
Question 166
A company is designing the layout of a new datacenter so it will have an optimal environmental temperature. Which of the following must be included? (Choose two.)
CorrectIncorrect -
Question 75 of 87
75. Question
Question 167
A user reports constant lag and performance issues with the wireless network when working at a local coffee shop. A security analyst walks the user through an installation of Wireshark and gets a five-minute pcap to analyze. The analyst observes the following output:
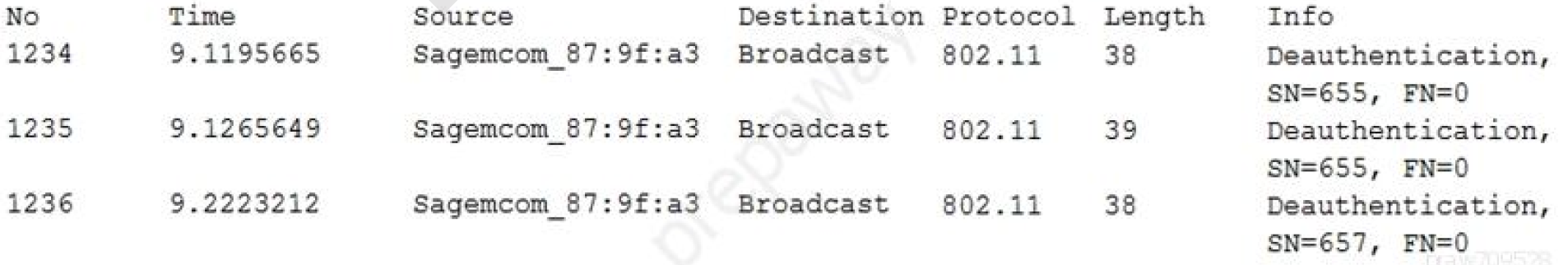 Which of the following attacks does the analyst MOST likely see in this packet capture?CorrectIncorrect
Which of the following attacks does the analyst MOST likely see in this packet capture?CorrectIncorrect -
Question 76 of 87
76. Question
Question 168
Which of the following would be BEST to establish between organizations to define the responsibilities of each party, outline the key deliverables, and include monetary penalties for breaches to manage third-party risk?
CorrectIncorrect -
Question 77 of 87
77. Question
Question 169
Users at an organization have been installing programs from the Internet on their workstations without first receiving proper authorization. The organization maintains a portal from which users can install standardized programs. However, some users have administrative access on their workstations to enable legacy programs to function properly. Which of the following should the security administrator consider implementing to address this issue?
CorrectIncorrect -
Question 78 of 87
78. Question
Question 171
A security engineer needs to implement an MDM solution that complies with the corporate mobile device policy. The policy states that in order for mobile users to access corporate resources on their devices, the following requirements must be met:
✑ Mobile device OSs must be patched up to the latest release.
✑ A screen lock must be enabled (passcode or biometric).
✑ Corporate data must be removed if the device is reported lost or stolen.
Which of the following controls should the security engineer configure? (Choose two.)
CorrectIncorrect -
Question 79 of 87
79. Question
Question 172
The facilities supervisor for a government agency is concerned about unauthorized access to environmental systems in the event the staff WiFi network is breached. Which of the following would BEST address this security concern?
CorrectIncorrect -
Question 80 of 87
80. Question
Question 173
A security analyst is reviewing information regarding recent vulnerabilities. Which of the following will the analyst MOST likely consult to validate which platforms have been affected?
CorrectIncorrect -
Question 81 of 87
81. Question
Question 174
A technician needs to prevent data loss in a laboratory. The laboratory is not connected to any external networks. Which of the following methods would BEST prevent the exfiltration of data? (Choose two.)
CorrectIncorrect -
Question 82 of 87
82. Question
Question 175
An organization routes all of its traffic through a VPN. Most users are remote and connect into a corporate datacenter that houses confidential information. There is a firewall at the Internet border, followed by a DLP appliance, the VPN server, and the datacenter itself. Which of the following is the WEAKEST design element?
CorrectIncorrect -
Question 83 of 87
83. Question
Question 176
After consulting with the Chief Risk Officer (CRO), a manager decides to acquire cybersecurity insurance for the company. Which of the following risk management strategies is the manager adopting?
CorrectIncorrect -
Question 84 of 87
84. Question
Question 177
A company’s Chief Information Security Officer (CISO) recently warned the security manager that the company’s Chief Executive Officer (CEO) is planning to publish a controversial opinion article in a national newspaper, which may result in new cyberattacks. Which of the following would be BEST for the security manager to use in a threat model?
CorrectIncorrect -
Question 85 of 87
85. Question
Question 178
A database administrator needs to ensure all passwords are stored in a secure manner, so the administrator adds randomly generated data to each password before storing. Which of the following techniques BEST explains this action?
CorrectIncorrect -
Question 86 of 87
86. Question
Question 179
The website http://companywebsite.com requires users to provide personal information, including security question responses, for registration. Which of the following would MOST likely cause a data breach?
CorrectIncorrect -
Question 87 of 87
87. Question
Question 180
An organization relies on third-party video conferencing to conduct daily business. Recent security changes now require all remote workers to utilize a VPN to corporate resources. Which of the following would BEST maintain high-quality video conferencing while minimizing latency when connected to the VPN?
CorrectIncorrect
